-
 NUAGE PEMF DEVICESPEMF FULL BODY MAT
NUAGE PEMF DEVICESPEMF FULL BODY MAT
PEMF MINIMAT
PEMF RING
PEMF FACE MASK
PEMF PULSEPAD
PEMF MEDALLION
-
-
 Hypertension (high blood pressure)
Hypertension (high blood pressure)
Arrhythmia
Poor blood supply(diabetic foot, ulcer)
Stroke
Parkinson’s disease
Sciatica
Spinal injuries
Multiple sclerosis
Stress
Depression
Fractures
Pseudoarthrosis (nonunion)
Osteoporosis
Osteoarthrosis (osteoarthritis)
Ligament injuries
Frozen shoulder
Tennis or golf elbow
Fibromyalgia
Asthma
Psoriasis
NUAGE PEMF HEAL MEDICAL CONDITIONSMore Medical Conditions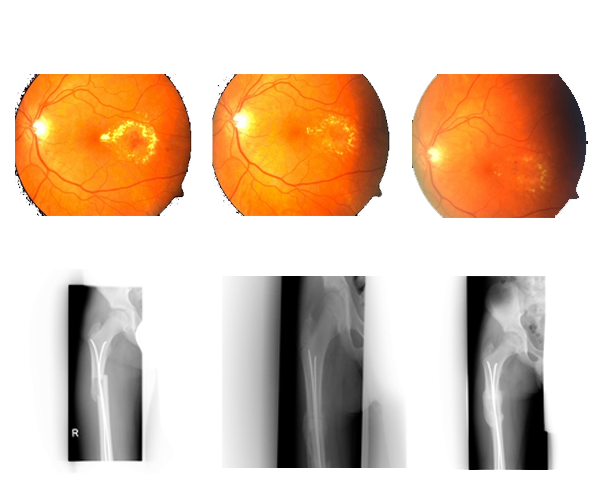 Diabetic RetinopathyFractured Femur & Pelvis
Diabetic RetinopathyFractured Femur & Pelvis
+91 11 4010 9681support@nuagehealth.in162,Chamber -II, Bhikaji Cama Place New Delhi- 110066
Spyrix
Two weeks later, Spyrix flagged unusual behavior. Mark was accessing client files outside his role, taking screenshots of spreadsheets, and emailing them to an external address disguised as “backup.” The software’s keystroke logging revealed he was deleting sent emails immediately — but Spyrix had already captured everything.
Sarah was relieved, not punished. The software had saved her — and the company — from disaster. spyrix
After research, she installed — a stealthy employee monitoring tool — on all company laptops. She announced it transparently in a revised IT policy: “To protect client confidentiality, all devices may be monitored for security purposes. Use of work devices for personal matters is not restricted, but all activity is logged.” Two weeks later, Spyrix flagged unusual behavior
She then offered every employee a clear copy of monitoring logs upon request, and set up a whistleblower channel for ethical concerns. Productivity didn’t plummet — it improved, because people knew that bad actors would be caught, but good employees would be protected. Monitoring software is neither good nor evil — it’s a tool. Used secretly and punitively, it breeds resentment. Used transparently, with clear policies and proportional responses, it can prevent leaks, protect employees from honest mistakes, and preserve integrity. The key is not the software’s power — but the purpose behind it. The software had saved her — and the
A month later, the IT manager, Priya, noticed another alert — not malicious, but concerning. An employee in accounting, Sarah, had accidentally copied unencrypted tax records onto a USB drive she then lost. Spyrix logged the USB connection and flagged the file transfer as “high risk.” Within an hour, Priya remotely locked the USB’s data and helped Sarah retrieve it before any breach occurred.





